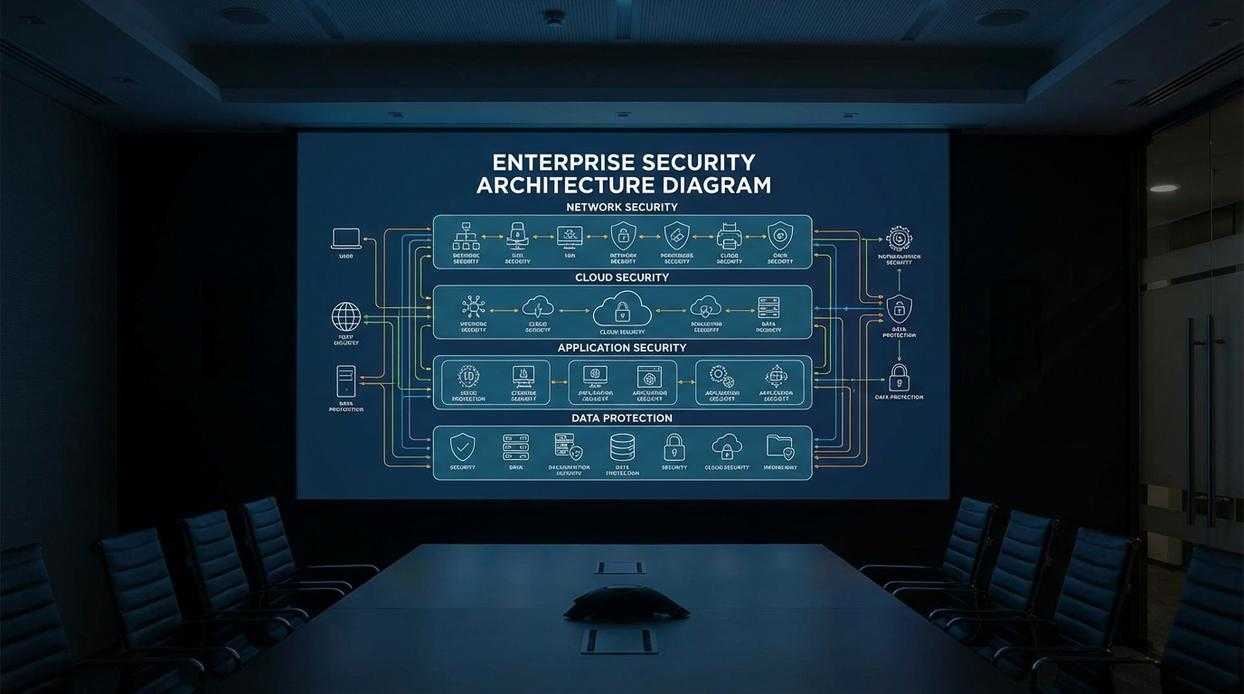
In today’s digital environment, an ad-hoc IT setup isn’t just inefficient—it’s a serious liability. Organizations that rely on reactive fixes rather than structured defenses face escalating risks, from data breaches to costly downtime. This article delivers a practical, step-by-step blueprint for building resilient cybersecurity infrastructure frameworks that protect your operations from the ground up. You’ll gain a clear, actionable roadmap covering risk assessment, secure architecture design, data protection strategies, and incident response planning. By the end, you’ll understand how to shift from patchwork security measures to a proactive, fortified digital infrastructure built to withstand evolving threats.
Pillar 1: Foundational Risk Assessment and Asset Management
The first principle is simple: you cannot protect what you do not know you have. In practice, that means building a comprehensive inventory of every digital and physical IT asset—hardware, software, databases, APIs, user accounts, and cloud workloads. If a forgotten server is still running in a closet (yes, that still happens), it’s a liability.
Start by cataloging assets by category, owner, location, and business function. Then, classify data sensitivity. For example, a public marketing site carries different risk than a customer payment database. Pro tip: automate discovery tools wherever possible to reduce human blind spots.
Conducting a Threat & Vulnerability Analysis
Next, map likely threats—ransomware, insider misuse, misconfigurations—to specific assets. Evaluate both likelihood and business impact. If your CRM goes down for 48 hours, what does that cost in revenue and reputation? This structured review aligns with established cybersecurity infrastructure frameworks and prevents guesswork.
Finally, establish a single source of truth: a centralized, continuously updated asset management system. Without it, security decisions become fragmented. This is especially critical when implementing hybrid it models balancing on premise and cloud systems, where visibility gaps multiply. In short, clarity first—defense second.
Pillar 2: Architecting a Zero-Trust Access Control Framework
A few years ago, I helped a mid-sized company investigate a breach that started with a single over-permissioned account. What should have been a minor phishing incident turned into a full database exposure because that user had admin rights “just in case.” That experience cemented my belief in the Principle of Least Privilege (PoLP)—the idea that every user, device, and application gets only the minimum access required to do its job. When you limit permissions, you shrink the blast radius, a term meaning the total potential damage from a compromise. In practice, that means marketing can’t access production servers, and service accounts can’t modify financial records.
However, PoLP alone isn’t enough. Credentials leak; phishing kits are sold like concert tickets. That’s why Multi-Factor Authentication (MFA) is non-negotiable. MFA requires two or more verification factors—something you know (a password), something you have (an app-based code or hardware key), or something you are (biometrics). Even if attackers steal passwords, hardware security keys can block automated attacks cold. Enforce MFA on VPNs, cloud dashboards, email, and especially privileged accounts. Pro tip: start with administrators, then expand outward.
Finally, Role-Based Access Control (RBAC) ties it all together. Instead of assigning permissions individually, you create predefined roles—HR, Finance, DevOps—with consistent access rules. This simplifies onboarding and offboarding and aligns cleanly with cybersecurity infrastructure frameworks. Some argue RBAC is rigid, but in reality, clarity beats chaos every time (ask anyone who’s untangled legacy permissions) during rapid organizational growth.
Pillar 3: Defining and Enforcing Secure Network & Data Protocols
Strong cybersecurity starts with intentional structure, not just expensive tools. If your network is a single open floor plan, attackers can roam freely once inside (think heist movie, minus the cool soundtrack). That’s where segmentation comes in.
Network Segmentation and Firewall Policies
Network segmentation means dividing your infrastructure into smaller, isolated zones so threats can’t move laterally. For example, your finance systems shouldn’t sit on the same segment as guest Wi‑Fi. If one zone is compromised, the blast radius stays contained.
Pair this with a deny-by-default firewall policy. This means all traffic is blocked unless explicitly allowed. Some argue this slows operations. In reality, it enforces discipline and visibility—two pillars highlighted across major cybersecurity infrastructure frameworks. Convenience is tempting, but exposure is costly.
Pro tip: Review firewall rules quarterly. Permissions tend to accumulate quietly.
Data Encryption Protocols (In-Transit and At-Rest)
Encryption protects data in two states:
- In-transit: Data moving across networks, secured using TLS/SSL.
- At-rest: Stored data on servers or devices, protected with AES-256.
Some teams believe perimeter defenses are enough. They’re not. If attackers bypass your firewall, encryption ensures stolen data remains unreadable. Both layers are essential.
Developing a Data Classification Policy
Not all data deserves equal protection. Create clear categories:
- Public
- Internal
- Confidential
- Restricted
Restricted data—like financial records—requires the strictest controls.
What’s next? Once classification is defined, align access controls and monitoring rules accordingly. Structure first. Enforcement second. Continuous review always.
Pillar 4: Continuous Monitoring and Incident Response Readiness
Security isn’t a “set it and forget it” firewall (if only). The need for proactive monitoring means using tools that track suspicious logins, unauthorized configuration changes, and anomalous traffic in real time. According to IBM’s Cost of a Data Breach Report, organizations with mature monitoring reduce breach costs significantly (IBM, 2023). So, implement continuous logging aligned with cybersecurity infrastructure frameworks and review alerts daily—not quarterly.
Next, build an Incident Response Plan before chaos hits:
- Detection
- Containment
- Eradication
- Recovery
Test it twice yearly (yes, like a fire drill). Pro tip: assign named owners to each phase.
Activating Your Security Strategy for Long-Term Defense
By implementing Assessment, Access Control, Protocol Enforcement, and Monitoring, you now have a clear, actionable framework to strengthen your cybersecurity infrastructure from the inside out. Your goal was long-term defense—not quick fixes—and this roadmap delivers the structure needed to reduce risk, close gaps, and stay resilient against evolving threats.
Remember, security weaknesses don’t appear overnight—they grow from overlooked assets and inconsistent oversight. The fastest way to take control is to act now.
Start with a complete IT asset inventory today. This single move lays the groundwork for every other protection layer. Organizations that follow structured security frameworks reduce breach risks significantly—don’t wait until vulnerabilities become incidents. Take the first step and secure your environment now.