Does it feel like cyber threats are closing in from all sides, leaving you scrambling? You’re not alone. Many businesses, swamped by data breaches and ransomware, are stuck reacting instead of planning.
It’s chaos. But here’s the catch: reacting without a plan only widens the gaps in your defenses.
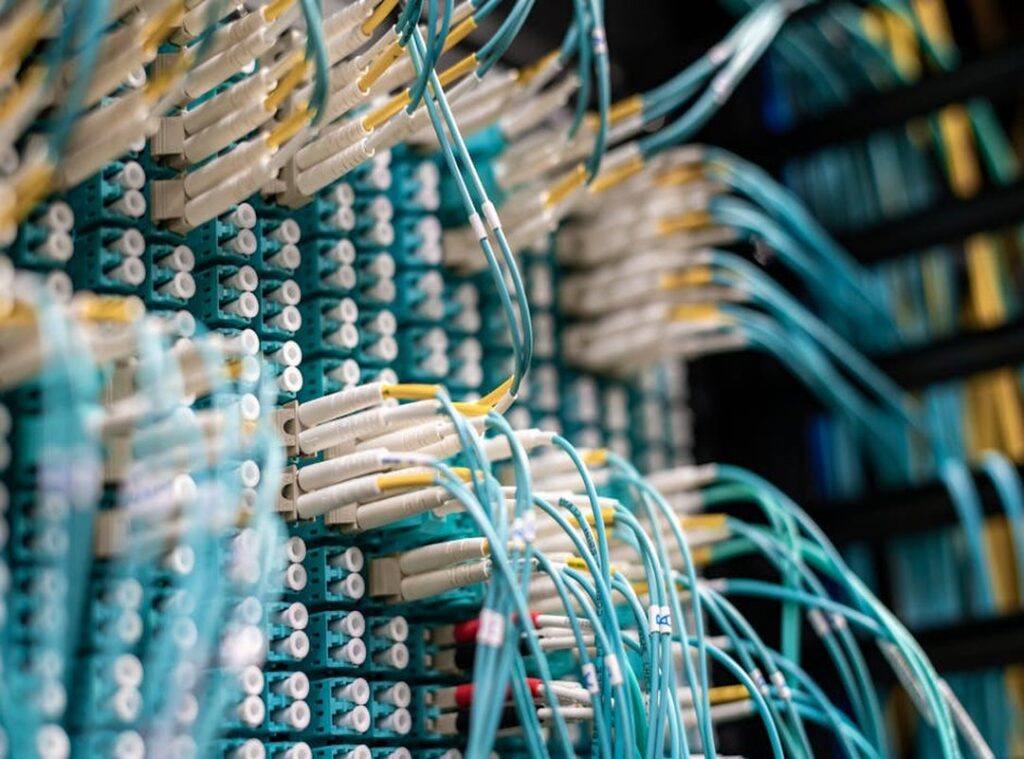
I can’t stress enough how important it is to have a cybersecurity digital infrastructure that’s not just a checklist but a resilient system. This isn’t some vague concept. I’ve spent years entrenched in digital infrastructure, understanding what it takes to secure it from the ground up.
So, what will you get from this article? We’ll break down the mystery of a digital security system and give you a practical blueprint. You’ll learn not just what it is, but how to build one that truly works.
Digital Security System: A Blueprint for Safety
So, what’s a digital security system? Imagine building a skyscraper. You wouldn’t just throw bricks and glass together.
You’d need a blueprint, right? That’s exactly what a digital security system is (an) architectural plan for your cybersecurity digital infrastructure. It’s not just an IT policy or a checklist.
It’s a changing guide that makes sure everything works together smoothly.
Think of it as managing cybersecurity risks in a structured, repeatable way. One that can evolve with new threats. Is it just a dry document like some policy gathering dust?
No. It’s a living plan key for making informed decisions. Can a mere checklist adapt when chaos strikes?
Didn’t think so.
What’s the point of it all? Simple. Better risk management, meeting regulatory requirements, and building trust with customers.
Not to mention, saving money on security in the long run. the magic happens (spending) efficiently instead of haphazardly.
But there’s more. A solid system helps businesses integrate strategies for optimizing cloud infrastructure maximum efficiency. It’s about keeping everything running like a well-oiled machine.
Got it? It’s not just about tech. It’s about peace of mind, knowing every part of your security plan works together seamlessly.
So, next time someone says “we have an IT policy,” ask them (do) they have a system? Because there’s a big difference. Trust me, the depth of strategic planning makes all the difference when it comes to cybersecurity.
Who wouldn’t want that level of protection?
The 5 Pillars: Cybersecurity System Fundamentals
Ever wondered what makes up the universal “DNA” of security frameworks? It’s simpler than it seems. Everything boils down to five core principles, inspired by the NIST Cybersecurity System.
They’re like the Avengers of digital protection: Identify, Protect, Detect, Respond, and Recover.
Let’s start with Identify. It’s all about knowing what you’re up against. Got assets?
You need to know where they are and what’s at risk. Think of it like setting the best defense in a game. Who’s playing, and where’s the ball going?
Without this step, you’re swinging at shadows.
Now, on to Protect. This is your shield. It’s where you put up barriers and controls to keep potential threats at bay.
Access control, data security, training (these) are your front-line defenders. Remember, even a fortress is useless if no one’s guarding it.
Detect is your early warning system. This is about finding threats before they can harm. Monitoring and anomaly detection are key here.
It’s like having security cameras in your digital infrastructure, spotting intruders before they break in and not after.
Respond. Think of it as your game plan when things go south. This is key during an incident.
How do you contain the chaos and keep it from spiraling? A good plan here is like having a seasoned coach during a crunch time.
Finally, there’s Recover. It’s cleanup and getting back to normal. A plan to restore operations is important.
Without recovery, you’re stuck in a loop of disaster.
Having Response and Recovery plans ready before chaos strikes is key. Can’t emphasize this enough. It’s not just about the gear you have but how quickly you can get back on your feet.
And in this mix, understanding the role of cybersecurity experts in all this adds a layer of useful expertise. This isn’t just tech jargon. It’s your cybersecurity digital infrastructure’s lifeline.
Demystifying the Top Cybersecurity Frameworks
Let’s break down these well-known frameworks and how they relate to building strong digital infrastructures businesses. You’ve probably heard of NIST, ISO 27001, and CIS Controls. So why are they the go-to choices out there?

NIST Cybersecurity System
The NIST system (a real sweetheart in the cybersecurity world) is all about flexibility. Developed in the U.S., it’s particularly popular with key infrastructure. It’s a risk-based approach that adapts to your needs.
You know, kind of like one of those choose-your-own-adventure books where you get to decide what works best for you. If you’re all about keeping things flexible and adjusting as you go, this one’s a keeper.
ISO 27001
ISO/IEC 27001 takes a more international approach. It’s the big dog when it comes to information security management systems. You want formal certification?
Global recognition? This system’s got you covered, making it super practical for businesses operating internationally. It’s designed for those who aim to impress with full security structures.
CIS Controls
Now, if you’re looking for a “get going now” system, look no further. CIS Controls offers actionable steps. Think of it as the fast food of the cybersecurity frameworks (quick,) straightforward, yet effective.
It prioritizes actions to mitigate common attacks. If you want to dive in without overthinking, CIS is your friend (no frills, just business).
So how do they stack up? Here’s a quick comparison:
| System | Use Case | Scope | Prescriptiveness |
|---|---|---|---|
| NIST | Flexible adaptation | National | Low |
| ISO 27001 | Formal certification | Global | High |
| CIS Controls | Actionable steps | Universal | Medium |
Each of these frameworks caters to different needs. Building Strong Digital Infrastructures Businesses often involves a mix of strategies. There’s no one-size-fits-all, so what do you need most?
Architecting Your Security System: A 4-Step Blueprint
Ever felt overwhelmed trying to protect your digital assets? I get it. Shifting from theory to action in cybersecurity isn’t easy.
But you can do it. Here’s how.
First up, assess your current state. You need to know what you’re working with. Conduct a risk assessment and inventory those digital assets.
After all, you can’t protect what you don’t know you have.
Next, define your goals and scope. What are you trying to achieve? Are you aiming to meet regulatory requirements like GDPR or HIPAA?
Maybe you’re looking to boost customer trust? Figure out which parts of your business need coverage. This isn’t just about ticking boxes.
It’s about real protection.
Step three, choose and customize your system. Don’t just adopt a generic model. Start with something like CIS Controls or the NIST CSF.
Tailor it to fit your specific risks and resources. Personalization is key.
Finally, set up and measure. This isn’t a one-and-done deal. Frameworks need continuous improvement.
Monitor your systems and adapt as threats evolve. It’s like maintaining a garden; constant attention is key.
Building a strong cybersecurity digital infrastructure isn’t just a task. It’s a journey. But with these steps, you’re on the right path.
Take Control of Your Digital Future
The world of cybersecurity can feel like wandering in the dark. We’re not just talking about buying shiny new tools. It’s about crafting a plan that transforms chaos into order.
With a solid digital security system, you’re not stumbling around. You’re paving a secure path forward.
Why risk waiting? Your business relies on a well-secured cybersecurity digital infrastructure. Start your risk assessment today.
Evaluate which system suits your business best. This isn’t just advice; it’s a necessity. Don’t leave your future to chance.
Take control now, and let security become your competitive advantage. Ready to secure your digital future?
 Cathleena Camachora has opinions about digital infrastructure strategies. Informed ones, backed by real experience — but opinions nonetheless, and they doesn't try to disguise them as neutral observation. They thinks a lot of what gets written about Digital Infrastructure Strategies, Expert Breakdowns, Tech Workflow Optimization Tips is either too cautious to be useful or too confident to be credible, and they's work tends to sit deliberately in the space between those two failure modes.
Reading Cathleena's pieces, you get the sense of someone who has thought about this stuff seriously and arrived at actual conclusions — not just collected a range of perspectives and declined to pick one. That can be uncomfortable when they lands on something you disagree with. It's also why the writing is worth engaging with. Cathleena isn't interested in telling people what they want to hear. They is interested in telling them what they actually thinks, with enough reasoning behind it that you can push back if you want to. That kind of intellectual honesty is rarer than it should be.
What Cathleena is best at is the moment when a familiar topic reveals something unexpected — when the conventional wisdom turns out to be slightly off, or when a small shift in framing changes everything. They finds those moments consistently, which is why they's work tends to generate real discussion rather than just passive agreement.
Cathleena Camachora has opinions about digital infrastructure strategies. Informed ones, backed by real experience — but opinions nonetheless, and they doesn't try to disguise them as neutral observation. They thinks a lot of what gets written about Digital Infrastructure Strategies, Expert Breakdowns, Tech Workflow Optimization Tips is either too cautious to be useful or too confident to be credible, and they's work tends to sit deliberately in the space between those two failure modes.
Reading Cathleena's pieces, you get the sense of someone who has thought about this stuff seriously and arrived at actual conclusions — not just collected a range of perspectives and declined to pick one. That can be uncomfortable when they lands on something you disagree with. It's also why the writing is worth engaging with. Cathleena isn't interested in telling people what they want to hear. They is interested in telling them what they actually thinks, with enough reasoning behind it that you can push back if you want to. That kind of intellectual honesty is rarer than it should be.
What Cathleena is best at is the moment when a familiar topic reveals something unexpected — when the conventional wisdom turns out to be slightly off, or when a small shift in framing changes everything. They finds those moments consistently, which is why they's work tends to generate real discussion rather than just passive agreement.